Information Security Incident Register Excel Template for ISMS
Original price was: ₹499.00.₹299.00Current price is: ₹299.00.
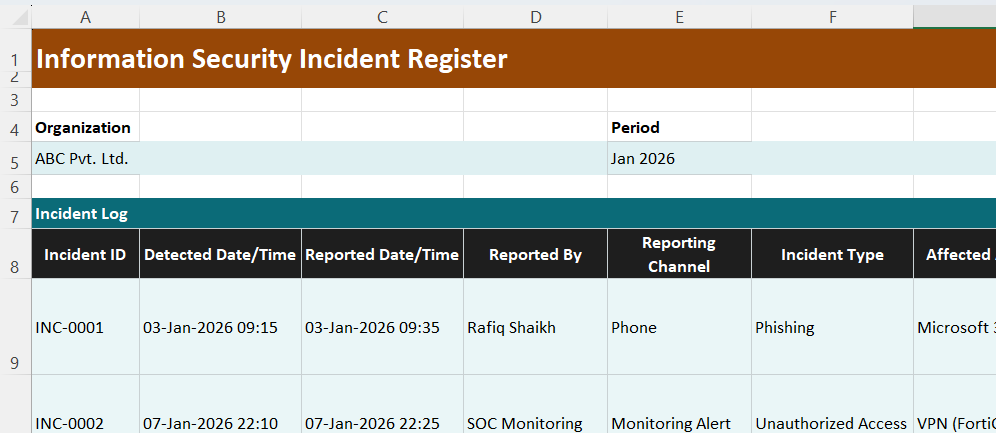
An audit-ready Incident Register in Excel. Log incidents with severity, CIA impact, actions, containment times, root cause, corrective actions, and closure status for ISMS reporting.
Description
The above image is only a preview. This downloadable Excel register standardizes incident logging. Moreover, it supports consistent classification and reporting. Therefore, it strengthens ISO 27001 incident management and SOC 2 monitoring. Also, it helps leadership track trends and closure discipline.
What does this Incident Register help you control?
First, you log detection and reporting details accurately. Then, you capture incident type and reporting channel. Also, you record affected assets and locations. Moreover, you classify severity and CIA impact consistently. Therefore, you prioritize response actions faster. Additionally, you document actions taken and containment timelines. Consequently, the register shows what happened and when.
Also, it tracks ownership and closure deadlines. Moreover, it captures target closure and actual closure dates. Therefore, teams reduce open items and delays. Furthermore, it supports root cause summaries and corrective actions. As a result, recurring incidents reduce over time.
How does this register support audits and reporting?
First, it creates a single source of truth for incidents. Then, it supports management reporting and KPI tracking. Also, it helps demonstrate response effectiveness. Moreover, it supports evidence sampling during audits. Therefore, audit time reduces and consistency improves. Additionally, it supports third-party incident tracking. Consequently, vendor governance becomes easier.
Also, it supports near-miss logging for proactive improvements. Moreover, it helps identify patterns across incident categories. Therefore, you can strengthen controls where needed. In addition, it improves cross-team coordination. Also, it aligns IT actions with compliance reporting.
Who should use this Incident Register?
This template suits ISMS owners and compliance leads. Also, it supports IT managers and SOC teams. Moreover, it helps risk and governance teams. Therefore, start-ups can build incident governance quickly. Additionally, SMBs can formalize documentation without heavy tools. Furthermore, larger teams can use it alongside SIEM outputs.
Also, it works for phishing, malware, data leakage, and access misuse. Moreover, it supports availability incidents and vendor issues. Therefore, it fits cloud services and on-premise systems. In addition, it supports ticket references for traceability. Also, it improves communication across IT, HR, and operations.
This register adds value over generic trackers. First, it enforces consistent fields for analysis. Then, it ties actions to owners and closure dates. Also, it produces audit-ready evidence with minimal effort. Therefore, incident reporting becomes reliable and decision-friendly.